MANAGED CYBERSECURITY.
ENGINEERED FOR RESILIENCE.
Active monitoring, response, and system stabilization for businesses that need real protection.
Environment Hardening
Threat Containment
Ongoing Oversight
Managed Detection & Response
We monitor for threats, investigate activity, and act when something happens.
We quickly contain and guide remediation to prevent spread or escalation.
We reduce recurring issues by keeping systems aligned and secure.
We continuously manage your security posture so nothing is left unattended.
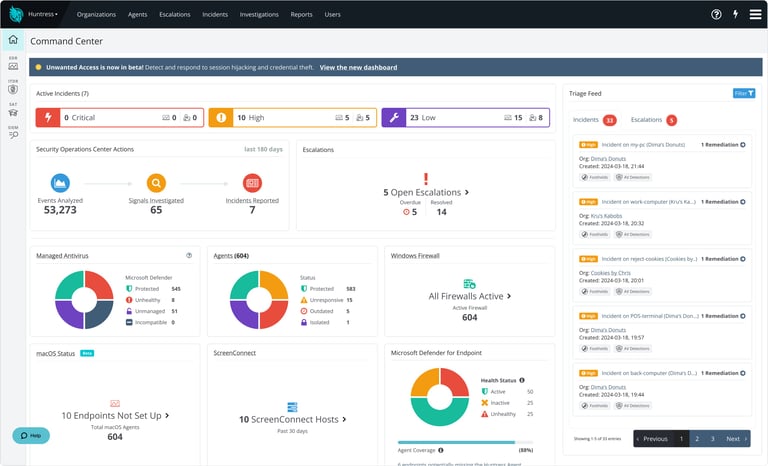
Managed EDR
Endpoint Detection & Response
Our Managed EDR solution delivers powerful, lightweight endpoint protection designed to stop ransomware, malware, and hands-on-keyboard intrusions. We continuously monitor for exploit attempts, persistence mechanisms, and suspicious behavior—automatically containing threats before they spread.
Includes:
Behavioral threat detection
Ransomware rollback & isolation
USB & application control
Automated policy management
SOC alerting & investigation
Weekly reporting
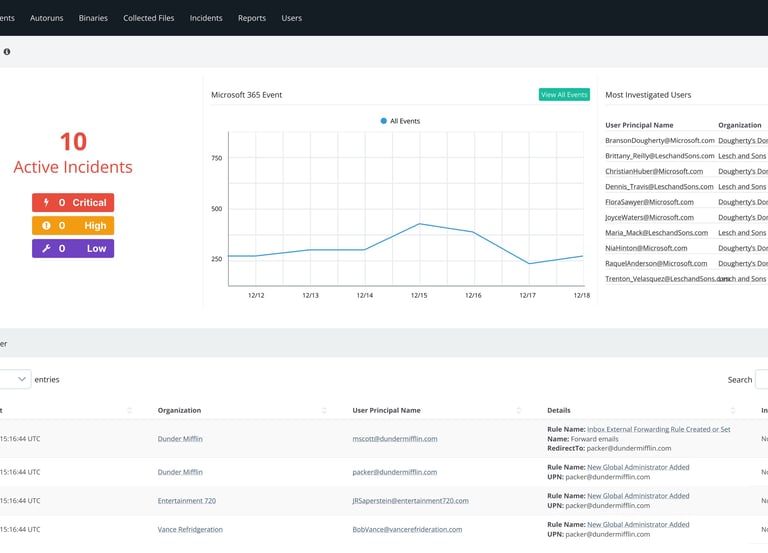

ITDR (Identity Threat Detection & Response)
Identity is the new perimeter—and attackers know it. Venom ITDR protects accounts from credential theft, account takeover attempts, MFA bypasses, and suspicious access patterns.
Includes:
Real-time identity monitoring
MFA enforcement & reporting
Detection of atypical logins
Password spray & credential stuffing detection
Compromised-account isolation
User behavior analytics
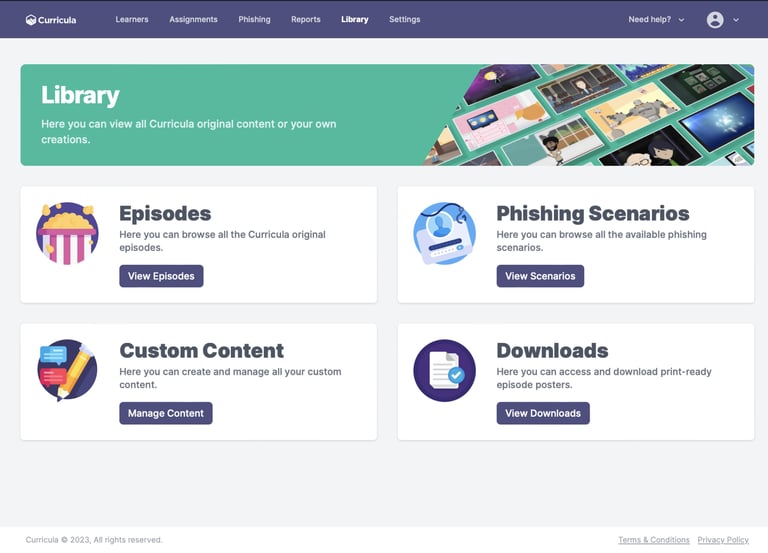
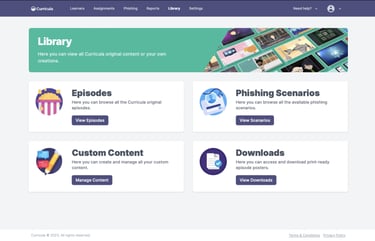
SAT (Security Awareness Training)
Human error is the #1 cause of breaches. Our SAT program trains employees to recognize phishing, social engineering, malware tricks, and insider risk. Includes automated campaigns, simulated phishing, and monthly micro-training.
Includes:
Monthly security training modules
Simulated phishing campaigns
User risk scoring
Policy acknowledgments
Training reports for compliance
Optional HIPAA/CMMC module packs
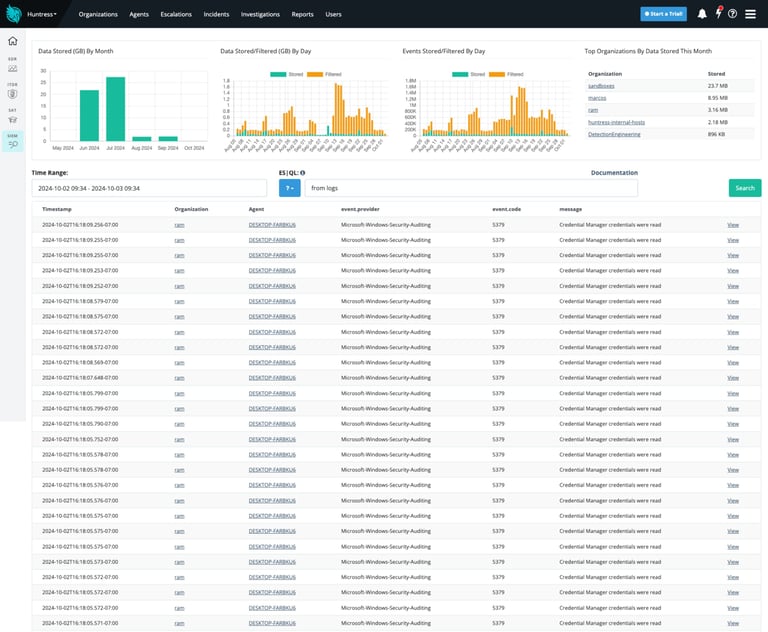
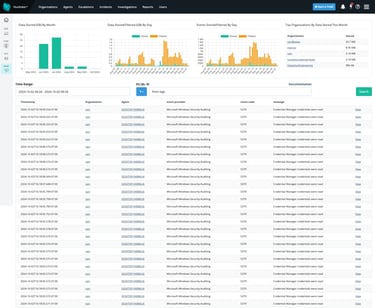
Managed SIEM (Security Information & Event Management)
Centralized log collection, analysis, and threat detection across your entire environment. Venom’s Managed SIEM correlates events from your endpoints, users, and systems to identify threats that slip past traditional tools.
Includes:
Log aggregation & retention
Real-time threat correlation
Alert triage & escalation
Compliance reporting (NIST, CMMC, HIPAA)
Weekly/monthly SIEM summaries
24/7 monitoring

